- What Is the Security Check?
- How to Run a Security Check
- Server and Software Versions
- Debug and Error Display
- User and Login Security
- Plugins and Themes
- Database and Credentials
- path security and Source Code
- File Access and Permissions
- Firewall and Protocol Security
- PHP Configuration
- WordPress Identity Leaks
- Frequently Asked Questions
- Related Tutorials
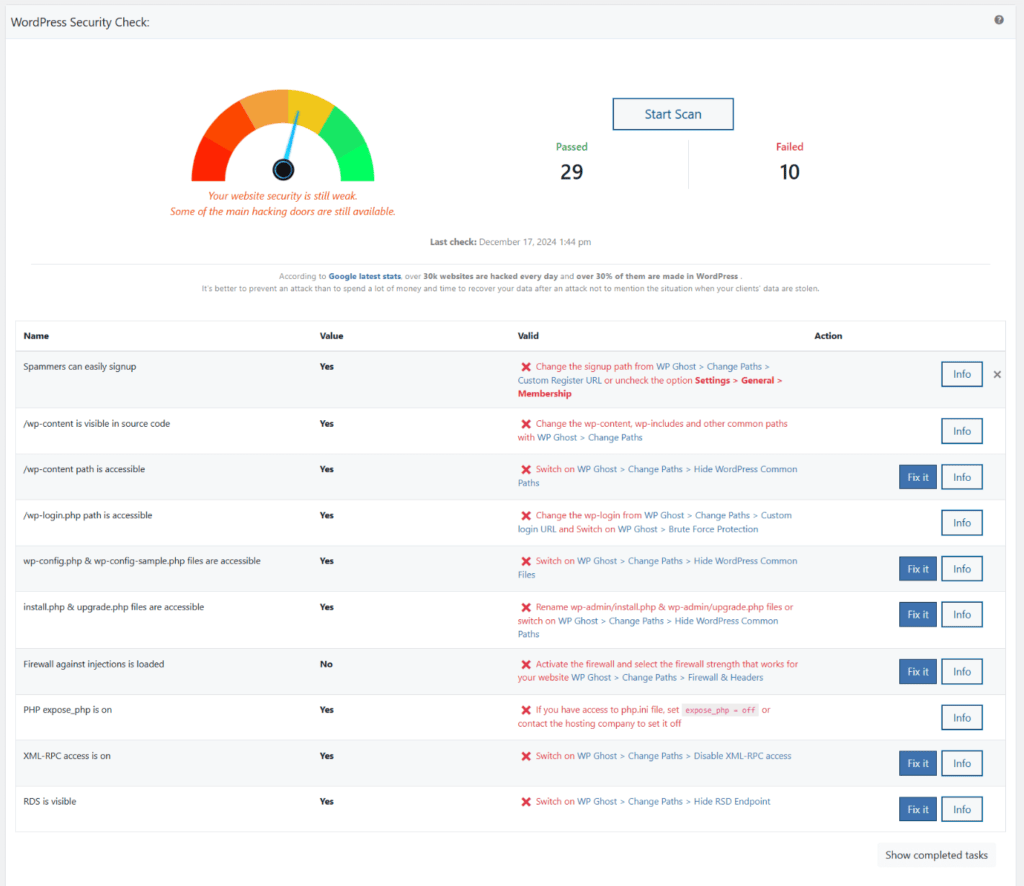
Run WP Ghost’s built-in security scanner to check 40 security tasks across your WordPress site, from outdated PHP versions to exposed login paths, and get specific instructions to fix every issue found. The Security Check scans your server configuration, WordPress settings, plugin/theme status, path visibility, file permissions, database security, PHP directives, and firewall status. Run it periodically to confirm your hack prevention configuration is complete. This is a free feature.
What Is the Security Check?
The Security Check is WP Ghost’s built-in scanner that runs 40 security tasks against your WordPress installation. It detects potential security breaches, identifies access issues before they become problems, checks whether your plugins and themes have known vulnerabilities, and tells you exactly which WP Ghost features to activate to fix each issue. It’s a checklist and a diagnostic tool in one.
How to Run a Security Check
Go to WP Ghost > Security Check and click Start Scan. WP Ghost runs all 40 tasks and returns a complete report with pass/fail status for each check and instructions to fix any issues found.
Run this periodically – after installing new plugins, updating WordPress, changing hosting, or modifying server configuration. A clean scan today doesn’t guarantee a clean scan after your next update.
Server and Software Versions
PHP Version – Checks that you’re running PHP 8.0 or higher. Older PHP versions have known, unpatched vulnerabilities and are a common factor in SQL injection attacks.
MySQL Version – Checks that you’re running MySQL 8 or higher (or MariaDB 10+). Outdated database versions have known vulnerabilities that enable SQL injection.
WordPress Version – Checks that WordPress is updated to the latest version. WordPress releases security patches regularly – sites running older versions are exposed to publicly known exploits.
Backend under SSL – Checks that the admin dashboard runs over HTTPS. Without SSL, login credentials are transmitted in plain text.
Debug and Error Display
These checks verify that debug modes are disabled on live sites. Debug output reveals file paths, plugin names, database structure, and PHP version – information that attackers use to plan targeted exploits.
WP Debug Mode – Checks that WP_DEBUG is off. Developers forget to disable it after development.
DB Debug Mode – Checks that database debug output is disabled on the live site.
Script Debug Mode – Checks that SCRIPT_DEBUG is off. When enabled, WordPress loads unminified scripts that reveal version information.
display_errors PHP directive – Checks that PHP errors aren’t shown to visitors. Errors should be logged silently, not displayed in the frontend.
User and Login Security
User “admin” as Administrator – Checks that no administrator account uses the username “admin.” This was WordPress’s default – half the login credentials attackers need for brute force.
Spammers can easily Signup – Checks whether open registration is enabled without protection. If you don’t need registration, disable it. If you do, activate Brute Force Protection on the registration form.
Author URL by ID access – Checks whether ?author={id} URLs reveal usernames. WordPress redirects these to /author/username/, exposing all usernames on your site to anyone who loops through IDs.
Plugins and Themes
Outdated Plugins – Checks for plugins with available updates. Outdated plugins are the #1 WordPress attack vector. 7,966 new vulnerabilities were disclosed in 2024 alone (Patchstack), and 43% were exploitable without authentication.
Not Recently Updated Plugins – Flags plugins that haven’t been updated by their developer in over 12 months. Abandoned plugins accumulate unpatched vulnerabilities.
Outdated Themes – Same check for themes. Theme updates fix security holes just like plugin updates.
Plugins/Themes editor disabled – Checks that the built-in code editor is disabled. The editor lets anyone with admin access inject malicious PHP directly into plugin and theme files.
Database and Credentials
Database Prefix – Checks that the table prefix isn’t the default wp_. The default prefix makes SQL injection attacks easier because bots know exactly which table names to target.
Salts and Security Keys valid – Checks that all 8 WordPress security keys (AUTH_KEY, SECURE_AUTH_KEY, LOGGED_IN_KEY, NONCE_KEY and their SALT counterparts) are properly set. These encrypt cookies and hashed passwords.
Security Keys Updated – Checks that keys have been regenerated recently. Stale keys should be renewed periodically for better security.
WordPress Database Password – Checks that the database password isn’t weak or empty. A strong database password prevents unauthorized database access even if the server is misconfigured.
path security and Source Code
These checks verify that WP Ghost’s path-security features are working – the core of your attack surface reduction strategy.
/wp-content path is visible in source code – Checks whether wp-content and wp-includes appear in the page source. Visible paths reveal your site as WordPress. Change paths with WP Ghost to hide them.
/wp-content path is accessible – Checks whether the original wp-content path still responds. Even after renaming, the old path should return 404 to prevent bot exploitation of plugin/theme vulnerabilities.
/wp-login.php path is accessible – Checks whether the default login page still responds. Hide the login path to block brute force bots targeting the default URL.
New Admin Path is visible in source code – Checks that your custom admin path doesn’t leak in source code or Ajax URLs. If exposed, bots can find your hidden admin and start brute-force attacks.
New Login Path is visible in source code – Same check for the custom login path. Keep it secret and activate Brute Force Protection.
Versions in Source Code – Checks whether WordPress, plugin, and theme version numbers appear in HTML source. Version tags help bots identify sites running vulnerable versions for Zero-Day Exploits.
File Access and Permissions
File Permission – Checks that critical files and folders have correct permissions. Incorrect permissions can allow unauthorized users to read, modify, or execute sensitive files. See How to Change File Permissions.
wp-config.php and wp-config-sample.php accessible – Checks that wp-config.php can’t be accessed directly via browser. This file contains database credentials, security keys, and other sensitive configuration.
readme.html accessible – Checks that readme.html is hidden. This file reveals the exact WordPress version, helping attackers target known vulnerabilities.
install.php and upgrade.php accessible – Checks that these admin files can’t be accessed externally. Attackers can exploit them to reinstall or overwrite your site.
Folder uploads is browsable – Checks that directory browsing is disabled for wp-content/uploads. If browsable, anyone can list and download all uploaded files.
Firewall and Protocol Security
Firewall against injections is loaded – Checks that WP Ghost’s firewall (7G or 8G) is active. Without a firewall, SQL injection and script injection attacks reach your database directly.
XML-RPC access is on – Checks whether XML-RPC is enabled. This protocol sends usernames and passwords in plaintext with every request. Disable it unless a specific plugin requires it.
PHP Configuration
These checks verify PHP server-level settings that affect security. Fixing these typically requires changes in php.ini or through your hosting panel.
register_globals is On – Checks that this deprecated PHP directive is disabled. When enabled, user input overwrites global variables – a direct path to code injection and privilege escalation.
expose_php is On – Checks that PHP version information isn’t exposed in HTTP headers. Knowing your PHP version helps attackers exploit version-specific vulnerabilities.
safe_mode is On – Checks that the deprecated safe_mode directive is off. It’s architecturally broken – it prevents legitimate functions from working while being trivially bypassed by attackers.
allow_url_include is On – Checks that this directive is disabled. When enabled, it exposes your site to remote file inclusion and cross-site scripting (XSS) attacks. There’s no valid reason to enable it.
WordPress Identity Leaks
Windows Live Writer is on – Checks whether the WLW Manifest link is present in the page header. If you’re not using Windows Live Writer (most sites aren’t), this link unnecessarily identifies your site as WordPress.
Default WordPress Tagline – Checks that you’ve changed the default tagline (“Just another WordPress site”). The default tagline immediately identifies your CMS to scanners.
Frequently Asked Questions
How often should I run the Security Check?
After every significant change: installing or updating plugins/themes, updating WordPress core, changing hosting providers, or modifying server configuration. As a minimum, run it monthly to catch configuration drift.
How do I fix failed checks?
Each failed check includes specific instructions in the scan results. Most can be fixed directly through WP Ghost settings – activate path security, enable the firewall, or toggle specific options in the Best Practice guide. Server-level checks (PHP directives, MySQL version) may require changes through your hosting panel.
Is the Security Check free?
Yes. The Security Check is available in the free version of WP Ghost. All 40 security tasks run regardless of whether you’re using free or Premium.
Does WP Ghost modify WordPress core files?
No. The Security Check reads configuration and tests access – it doesn’t modify any files. Fixes applied through WP Ghost settings use rewrite rules, WordPress filters, and mapping, not core file modifications.
Related Tutorials
Fix issues found by the Security Check:
- WP Ghost Settings Best Practice – Comprehensive configuration guide that addresses most Security Check findings.
- Customize Paths with WP Ghost – Fix path visibility issues flagged by the scanner.
- Firewall Security – Enable injection protection.
- Brute Force Protection – Protect login, registration, and comment forms.
- How to Change File Permissions – Fix permission issues.
- Change and Hide the Login Path – Fix exposed login path.
